The availability of Smartphones and other computing devices using commercial, network based operating systems in military use enable developers to introduce innovative solutions that add efficiency and improve processes, but also compromises organizations to exploitation by adversaries. When it comes to military organizations, such compromise can lead to defeat.
A recent example is ‘Попр-Д30.apk’, an artillery support app developed in 2013 by an officer of the Ukrainian 55th Artillery Brigade officer. As the filename suggested, the app relates specifically to the D-30 122mm towed howitzer, an artillery weapon first manufactured in the Soviet Union in the 1960s but still in use today. According to the developer Yaroslav Sherstuk, the application computes the traditional manual process of positioning, planning and firing tables, thus dramatically reducing the time to fire the D-30. Although the app was not distributed in the open, Sherstuk claim it had a user base of 9000 users. (A video covering the artillery units using the application is shown below).
In-depth reverse engineering by Crowdstrike revealed that the original application package was ‘contaminated’, probably as early as 2014, by a Trojan malware identified as an Android variant of X-Agent, the command and control protocol was closely linked to observed Windows variants of X-Agent, and utilized a cryptographic algorithm called RC4 with a very similar 50-byte base key.
The likely role of this malware is strategic in nature. The capability of the malware includes gaining access to contacts, Short Message Service (SMS) text messages, call logs, and internet data, and FANCY BEAR would likely leverage this information for its intelligence and planning value.
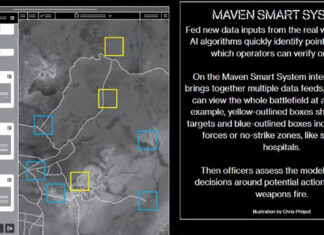
What was the purpose of this attack? According to Crowdstrike analysis, “successful deployment of the FANCY BEAR malware within this application may have facilitated reconnaissance against Ukrainian troops. The ability of this malware to retrieve communications and locational data from an infected device makes it an attractive way to identify the general location of Ukrainian artillery forces and engage them.”
Open source reporting indicates that Ukrainian artillery forces have lost over 50% of their weapons in the 2 years of conflict and over 80% of D-30 howitzers, the highest percentage of loss of any other artillery pieces in Ukraine’s arsenall. It is possible that the deployment of this infected app may have contributed to the high-loss nature of this platform.
The Trojan may not be the sole cause for this massive loss, but likely served to support the reconnaissance role of traditional battlefield assets. Although traditional overhead intelligence surveillance and reconnaissance (ISR) assets (drones) were likely still needed to finalize tactical movements, the ability of this application to retrieve communications and gross locational data from infected devices, could provide insight for further planning, coordination, and tasking of ISR, artillery assets, and fighting force.
A tool such as this has the potential ability to map out a unit’s composition and hierarchy, determine their plans, and even triangulate their approximate location. This type of strategic analysis can enable the identification of zones in which troops are operating and help prioritize assets within those zones for future targeting.
Mr Sherstuk denied the possibility the application he developed was hacked. On his Facebook page, he commented about the Crowdstrike report, saying it was “delusional and written for amateurs… So it is clear to everyone, distribution of the software is still under my control and is not in the public domain, and the activation is controlled personally by me,” the Telegraph wrote.
This previously unseen variant of X-Agent represents FANCY BEAR’s expansion in mobile malware development from iOS-capable implants to Android devices, and reveals one more component of the broad-spectrum approach to cyber operations taken by Russia-based actors in the war in Ukraine. Crowdstrike assessed that FANCY BEAR is likely affiliated with the Russian military intelligence (GRU), and works closely with Russian military forces operating in Eastern Ukraine and its border regions in Russia.
Attacked the US Democratic Committee used the same tools a cyber espionage group known as ‘Fancy Bear’ reportedly spied after Ukrainian artillery units using an infected application developed by a Ukrainian Army officer for use with Ukrainian artillery technical staff. The US based Crowdstrike that reported today on this attack identified the code that infected the app as X-Agent, the same malware used in the intrusions into the U.S. Democratic National Committee (DNC), and other political organizations.
Crowdstrike analysts assess the Ukrainian application is likely only the initial iteration of this type of malware. While it was initially discovered in a battlefield environment, an adversary could also leverage it in attacks against non-military targets. Mobile devices and internet-connected technology have increasingly proliferated civilian and military organizations. This technique may very likely be deployed in the political, government, or non-governmental sectors soon.