Empire Challenge (EC 09) sets the stage for an annual demonstration of intelligence, surveillance and reconnaissance (ISR) interoperability, executed by US Joint Forces Command (JFCOM) under the sponsorship of the Under Secretary of Defense for Intelligence (USD/I).
The exercise, hosted by the U.S. Navy Air Warfare Center Weapons Division, began July 6, 2009 and runs until the end of the month, at the Naval Air Weapons Station China Lake, California. While the real activity is taking place at China Lake, other locations throughout the world are taking part in the process of collecting, processing and distributing the data, turning it into situational analysis and comprehending. Locations taking part in the exercise include the Joint Intelligence Lab in Suffolk, Va., the Combined Air Operations Center-Experimental at Langley Air Force Base, Hampton, Va., service Distributed Common Ground/Surface System (DCGS) labs, coalition sites in the United Kingdom, Canada, Australia and the NATO Consultation, Command and Control Agency in the Netherlands.

The exercise will provide an opportunity to evaluate and study how current and future ISR solutions could co-operate and to what level they meet the warfighter requirements, as identified by combatant commanders, services and coalition partners, to better support to command and control, enhance coalition data sharing and interoperability. The exercise will also examine and improve the interoperability between national/strategic ISR and tactical ISR. Among the technical goals set for the exercise are the evaluation of new data sharing techniques, demonstration of ‘multi-intelligence battlespace awareness’ and assessment of the DCGS Initial Capabilities Document and Concept of Operations version 2.
“EC09 focuses on improving interoperability with the distributed common ground systems (DCGS) and also looking at what new tools, capabilities and techniques we can bring into the fight to improve the situational awareness of our operational forces,” said Christopher Jackson, Integration Division chief at USJFCOM’s Joint Transformation Command for Intelligence and a principal investigator for EC09. DCGS is currently employed in different locations around the world by the US Air Force and the US Army. It uses a common set of services and data standards. The system utilized an Integrated Backbone (DIB), which allows data to be discovered and retrieved regardless of data location. The Distributed Development & Test Enterprise, an experimentation network built exclusively for DCGS, tests service DCGS interoperability.
In a terrain that vaguely resembles the Afghan mountainous desert, “Blue” forces are running convoy operations while “red” forces are setting up ambushes against them, using roadside and vehicle bombs, firing mortars against bases and logistics operations. The Blue forces are using airborne intelligence-gathering platforms are flying overhead including U-2 high-altitude reconnaissance aircraft, RQ-4 Global Hawk unmanned aerial vehicles and ScanEagle unmanned aircraft systems.
USJFCOM’s Joint Intelligence Laboratory (JIL) and the Combined Air Operations Center-Experiment at Langley Air Force Base, Va. conduct the modeling and simulation capabilities and analysis. Naval Air Weapons Station China Lake, Calif. hosts the demonstration’s more visual aspects. “China Lake is the tactical edge for this event,” said Air Force Col. Skip Krakie, EC09’s director for intelligence operations. “They offer us a fantastic range where we can conduct operations in realistic environment. It’s hot, dry and dusty. It’s everything Afghanistan is.”
By putting a demonstration through a laboratory alone, the results may not be the same if it is put into an environment that is operationally representative of what warfighters are facing today. “Things might not work as well or as crisply as they do within a compliant environment,” Jackson said. “EC09 is a proof of ISR capabilities before we take them into real world situations.”
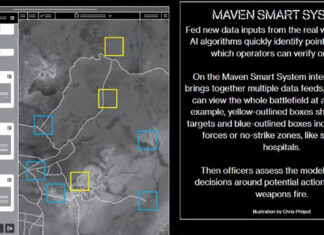
This year’s demonstration includes a virtual brigade combat team in addition to the live ISR assets. Both the live and the virtual assets are working together to form a combined task force that collects, analyzes and shares information. These ‘virtual entities’, created as computer generated forces representing much larger and complex scenarios. The exercise include specific scenarios to address joint capability threads. These include irregular warfare, joint ISR management, multi-domain awareness and ISR-strike integration. The scenarios were created in response to requirements from the field, as warfighters require improving ISR support addressing irregular warfare and counter-IED operations; strike operations; and persistent surveillance across multiple domains. The issue is not acquiring the sensor that can see the insurgent or IED, but finding superior ways to manage the available assets, in a way they are more likely to cover the right place at the right time, retrieve relevant information rapidly and better associate between pieces of information that create the entire picture.
Empire Challenge is working through some of those challenges in a highly realistic environment. Intelligence collected at China Lake or generated through computer modeling and simulation is fed to analysts at participating sites, who turn it around as quickly as possible. Evaluating different ways to delivering mission-critical ISR data to the warfighter, Empire Challenge is testing the interoperability, data sharing and distribution among the four US armed services and special operations command, coalition partners and allies. Once processed, ISR data is streamed to the command-and-control elements, representing the ‘user’ of such tactical information. By utilizing sophisticated networking, security and interoperability systems, this complex and, traditionally slow process could be accelerated and become more efficient, bringing valuable, time-critical intelligence to support the warfighter.